Cloud Notes: AWS TGW
updated: 1st of January 2024
published: 30th of December 2023
Intro
AWS Transit Gatway (TGW) is a network transit hub that simplifies interconnection of VPCs and on-premises networks.
Features
The following are some features of a TGW.
- A TGW is a highly available regionally resiliant service.
- The TGW supports transitive routing, therefore it removes the need for a full mesh of connections between VPCs and on-premises networks.
- Supports connectivity to VPCs, Site-to-Site VPN, Direct Connect (DX), other TGWs and 3rd Party NVAs via attachments.
- Can be peered across regions or across accounts.
- Can be shared between accounts using AWS Resource Access Manager (RAM).
- TGW peering connections are encrypted using AES-256 at the virutal network layer.
TGW Attachments
TGW attachments are used to connect resources to the TGW. There are 5 main types of attachments:
- VPC attachment - Connect VPCs to the TGW.
- VPN attachment - Connect Site-to-Site VPNs to the TGW.
- DX attachment - Connect DX to the TGW.
- Connect attachment - Connect 3rd party NVAs to the TGW.
- Peering attachment - Connect TGWs to each other.
TGW Architecture
The following diagram shows a typical TGW architecture.
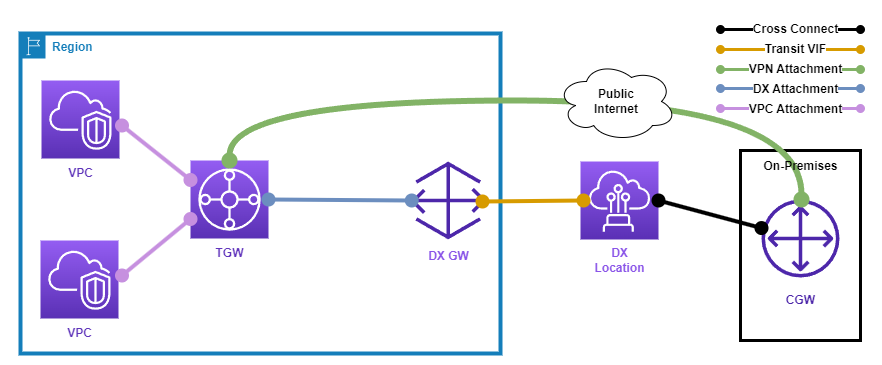
The following points describe the above diagram.
- The TGW is a hub connecting AWS VPCs and on-premises networks.
- The VPCs are connected to the TGW via VPC attachments
- The Customer Gateway (CGW) is connected to a DX Location via a physical cross connect.
- The DX Location is connected to the DX Gateway via a Transit VIF and a TGW association.
- The TGW is configured with a DX attachment.
- The CGW is connected to the TGW over the public internet via an IPSEC VPN.
- The TGW is configured with a VPN attachment for the AWS side of the the IPSEC VPN connection.
TGW Considerations
The following are some considerations when using a TGW:
- A TGW is a regional service, therefore it can be used to connect resources within a region.
- A TGW has a default route table that is automatically associated with all attachments.
- A TGW can have multiple different route tables, however only one route table can be associated with an attachment at a time.
- TGW peering connections currently exchange routes using static routes.
- Public to Private hostname resolution is NOT supported across inter-region TGW peering connections.
- TGW quotas can be found here.
TGW Connect
TGW Connect is a feature that allows you to connect 3rd party Network Virtual Appliances (NVAs) to the TGW. TGW connect utilizes GRE tunnels to connect the NVAs to the TGW and BGP to exchange routing information.
The following diagram shows a typical TGW connect architecture.
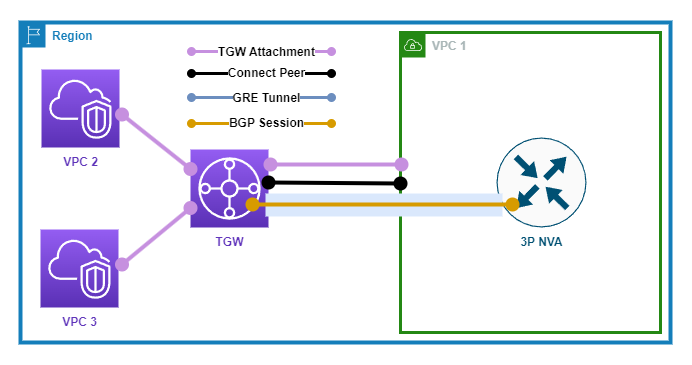
The following points describe the above diagram.
- The TGW is connected to 2x VPCs via VPC attachments.
- A Connect attachment is configured on the TGW to VPC 1.
- A GRE tunnel is configured between the NVA and the TGW.
- a BGP session is configured between the NVA and the TGW to exchange routing information.
Links
https://learn.cantrill.io/courses/1231680/lectures/33442228
https://docs.aws.amazon.com/vpc/latest/tgw/what-is-transit-gateway.html
https://docs.aws.amazon.com/vpc/latest/tgw/tgw-dcg-attachments.html
https://docs.aws.amazon.com/vpc/latest/tgw/transit-gateway-quotas.html